Advanced Electronic Data Wiping Techniques
Data destruction is a critical process for ensuring the security and privacy of electronic data. Simply deleting or reformatting a device is not enough to protect sensitive information. Advanced techniques are necessary to completely and securely erase data. In this article, we will explore the various methods of electronic data wiping, including data destruction, data sanitisation, and the importance of implementing these techniques in today’s digital landscape.
Importance of Data Destruction
Data destruction plays a critical role in protecting data privacy and preventing data breaches. For companies that heavily rely on electronic media for their business operations, implementing robust data destruction methods is not just a best practice, but also a legal requirement. Failure to properly destroy data can result in severe consequences, including legal action and irreparable harm to a company’s reputation.
In a recent study, it was discovered that a majority of hard drives still contained residual data even after deletion attempts. This startling finding underscores the necessity for organizations to adopt proper data destruction techniques to ensure the complete eradication of sensitive information.
“Effective data destruction methods are a crucial component of any comprehensive data security strategy. Failure to securely dispose of data can leave organizations vulnerable to data breaches and regulatory non-compliance.”
Data breaches are a significant concern in today’s digital landscape, with cybercriminals constantly seeking to exploit unprotected data. By implementing thorough data destruction processes, businesses can significantly reduce the risk of data breaches and protect the privacy of their customers and stakeholders.
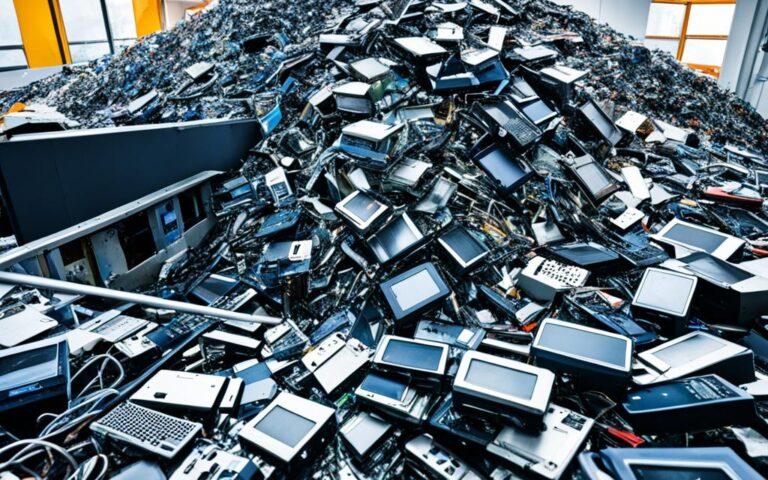
Note: Visual representation of data destruction techniques and security
Protecting Sensitive Information
Proper data destruction ensures that confidential information, such as customer details, financial records, and trade secrets, is permanently removed from electronic devices. In an era where data is a valuable commodity, organizations must prioritize the secure disposal of end-of-life devices, such as computers, servers, and mobile devices, to prevent unauthorized access.
Compliance with Legal Requirements
Various legal standards and regulations, such as the General Data Protection Regulation (GDPR) in Europe and the California Consumer Privacy Act (CCPA) in the United States, mandate the secure destruction of personal data. Failure to comply with these regulations can result in substantial financial penalties and reputational damage.
Preventing Data Recovery
Merely deleting files or formatting storage devices does not guarantee the permanent removal of data. Sophisticated tools and techniques can recover deleted or formatted data, posing a significant risk to the security of sensitive information. Proper data destruction methods, such as overwriting data with random patterns, ensure that residual data cannot be recovered.
Peace of Mind
By investing in effective data destruction practices, organizations can have peace of mind, knowing that their sensitive information is safely disposed of. This not only instills trust among customers and partners but also protects the organization’s reputation in an increasingly data-centric world.
Different Data Destruction Types
When it comes to data destruction, there are several different methods available, each with its own level of effectiveness and suitability for specific situations. Understanding these data destruction types is crucial for organizations that want to ensure complete eradication of sensitive information.
Deleting/Reformatting
Deleting or reformatting a device may seem like a simple solution to get rid of data. However, this method only removes the data from file folders and doesn’t completely erase it from the memory chip or hard drive. Therefore, it leaves the data vulnerable to recovery by malicious entities.
Wiping
To make data unreadable and irretrievable, wiping is employed. This method involves overwriting the existing data, replacing it with random characters or predefined patterns of ones and zeroes. By doing so, wiping ensures that the original data is permanently removed and cannot be recovered.
Overwriting
Similar to wiping, overwriting also involves replacing existing data with new information. However, overwriting follows a set pattern of ones and zeroes. This method can effectively remove data, but the number of passes required to ensure complete erasure may vary depending on the sensitivity of the data and the organization’s security protocols.
Erasing
Erasing is another method that aims to render data irretrievable. It is similar to overwriting, but it goes a step further by providing a certificate of destruction. This certificate serves as proof that the data has been completely removed and cannot be recovered, providing organizations with an added level of assurance.
Degaussing
Degaussing is a unique data destruction method that focuses on destroying computer data by eliminating magnetism. By subjecting the device to strong magnetic fields, degaussing permanently erases the data, making it unrecoverable. This method is commonly used for media types that store data magnetically, such as hard drives and magnetic tapes.
Physical Destruction
In some cases, physical destruction is required to ensure data security. This method involves physically destroying the device, such as smashing a hard drive or shredding it into small pieces. Physical destruction guarantees that the data is permanently destroyed beyond any possibility of recovery.
Shredding
Shredding is a common method used for destroying physical storage devices. Implemented through an industrial machine, it effectively shreds drives into small pieces, making data retrieval impossible. Shredding is often employed for hard drives, CDs, DVDs, and other physical media to ensure complete data destruction.
“Proper selection of the data destruction method is crucial to maintain data security and prevent unauthorized access to sensitive information.”
DoD 5220.22-M Data Wiping Standard
The DoD 5220.22-M data wiping standard, established by the US National Industrial Security Program, is a widely used method within data destruction software. This standard involves a rigorous three-pass procedure that overwrites data with specific patterns of ones, zeros, and random characters. While it was once widely accepted, the DoD 5220.22-M standard is now considered less effective and resource-demanding compared to more modern standards like NIST 800-88.
Although the DoD 5220.22-M standard may not be the most advanced option available, its historical significance and credibility mean that some organizations still require compliance with this standard for data erasure processes.
Conclusion
Ensuring data security and privacy protection is paramount in today’s digital landscape, and advanced electronic data wiping techniques play a crucial role in achieving these goals. By utilizing a combination of deleting/reformatting, wiping, overwriting, erasing, degaussing, physical destruction, and shredding, organizations can effectively eliminate data and prevent unauthorized access.
While the DoD 5220.22-M standard was once widely used, newer standards like NIST 800-88 are now recognized as more effective data destruction methods. It is imperative for businesses to adopt these advanced techniques to stay ahead of potential security threats and comply with data security regulations.
By implementing reliable data destruction methods, organizations can safeguard against data breaches, protect proprietary information, and maintain customer trust. Privacy protection is especially crucial for companies that rely on electronic media for their operations, as failure to securely destroy data can result in severe legal and reputational consequences.
Ultimately, businesses must prioritize data security and privacy by investing in advanced electronic data wiping techniques. With the right approach to data destruction, organizations can confidently handle sensitive information, mitigate the risk of data breaches, and uphold their commitment to protecting privacy.
FAQ
What is data destruction?
Data destruction is the process of rendering data completely irretrievable from electronic devices.
Why is data destruction important?
Data destruction is important for protecting data security and preventing data breaches. It is crucial for companies that rely on electronic media for their business operations.
What are the different types of data destruction methods?
The different types of data destruction methods include deleting/reformatting, wiping, overwriting, erasing, degaussing, physical destruction, and shredding.
What is the DoD 5220.22-M data wiping standard?
The DoD 5220.22-M data wiping standard is a method used in data destruction software. It involves a three-pass procedure of overwriting data with specific patterns of ones, zeros, and random characters.
Are there more modern data wiping standards available?
Yes, more modern standards like NIST 800-88 are considered more effective compared to the DoD 5220.22-M standard.