The Benefits of Secure Electronic Disposal
In today’s digital age, data privacy and environmental sustainability have become paramount concerns for businesses. Secure electronic disposal offers a solution that addresses both of…

In today’s digital age, data privacy and environmental sustainability have become paramount concerns for businesses. Secure electronic disposal offers a solution that addresses both of…
Transparency is essential in the laptop recycling process to address global concerns about electronic waste pollution and promote sustainable tech usage and ethical disposal. Both…

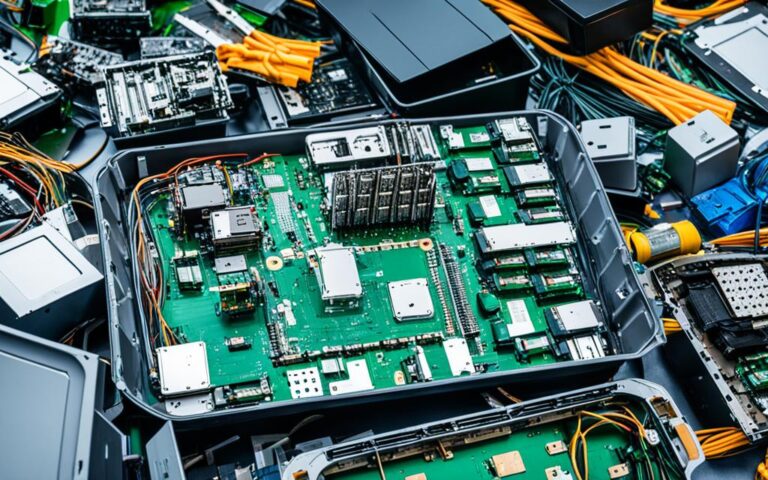
According to recent data, e-waste, including end-of-life electronics like laptops, presents a significant global environmental challenge. In fact, it is estimated that over 57 million…

Data hoarding psychology poses significant challenges to effective data disposal. Many individuals find it difficult to let go of their digital clutter, leading to an…

Laptop recycling has a significant impact on the environment and society. As technology advances and laptops become more prevalent, the need for proper disposal and…
In a world where sustainability and tech progress are paramount, the circular economy has emerged as a transformative model. By reimagining the lifecycle of electronic…

In today’s rapidly evolving technological landscape, responsible disposal of servers and network equipment is crucial for data security and resource management. Server recycling initiatives have…

Preventing data breaches is a critical concern for businesses in today’s digital landscape. As technology evolves, so do the potential risks and vulnerabilities associated with…

In today’s digital era, the retirement of IT assets has become a crucial process for UK businesses. IT asset retirement involves securely retiring IT assets…

Server recycling plays a crucial role in reducing environmental impact and achieving net-zero targets. In today’s world, where technology is constantly evolving, it is essential…

Protecting sensitive information is of utmost importance in today’s digital age. As technology advances, so do the risks of data breaches and identity theft. To…

Recycling old laptops is not only beneficial for the environment but also has a significant impact on the lives of jobseekers. Through initiatives like the…

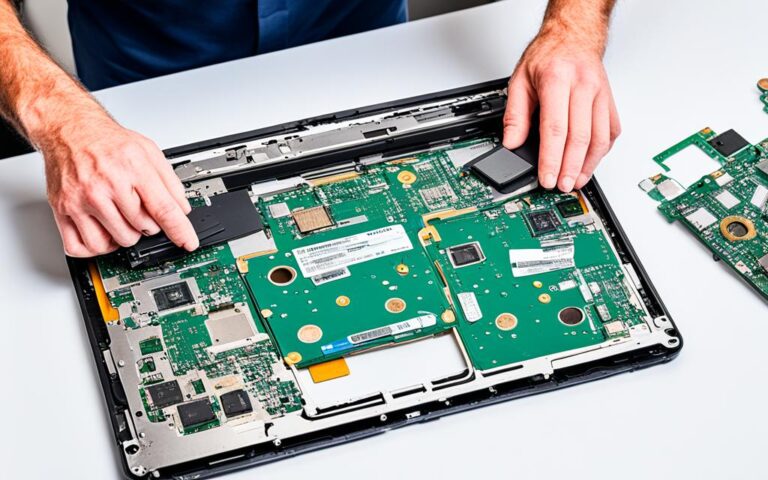
Refurbishing PC components offers a sustainable approach to computing by extending the life cycle of devices and reducing electronic waste. In today’s technology-driven world, where…

In today’s digital age, UK businesses face the challenge of securely disposing of outdated PC workstations while ensuring responsible recycling practices. The confidential data stored…

Mobile devices have become an integral part of our lives, and with the constant advancements in technology, we often find ourselves replacing our devices with…

In today’s digital age, access to technology and the internet is crucial for economic, educational, and social opportunities. However, not everyone has equal access, leading…

Data destruction is an essential element in litigation avoidance, helping businesses in the UK mitigate legal risks and protect sensitive information. By strategically implementing data…

In today’s fast-paced world, data centres are a crucial component of our digital infrastructure. However, as technology rapidly evolves, data centres must adapt and upgrade…

Recycling Challenges Phones Tablets “The journey towards a greener future begins with overcoming the challenges of recycling phones and tablets. As technology advances at an…

Upgrade your desktop with purpose and join the sustainable business stream. At Techbuyer, we believe in extending the life of your IT devices through desktop…

As laptops have become an integral part of our lives, it’s important to address the environmental impact they have on our planet. The production, use,…