Reimagining Components: The Art of Desktop Component Reuse
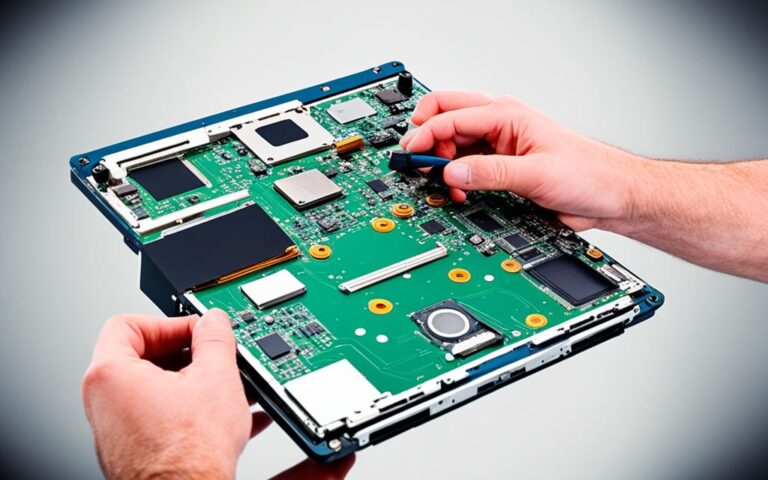
In today’s rapidly evolving technological landscape, sustainable computing has become an essential consideration for businesses and individuals alike. One innovative approach to achieving sustainability is…